Found a hole in Bluetooth, which allows you to hack the device with the operating system Apple and Microsoft
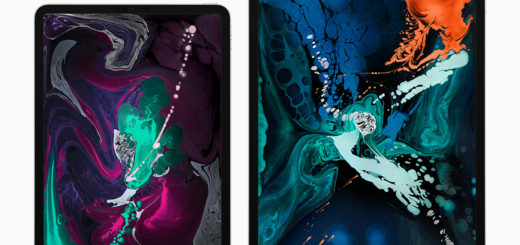
Researchers at Boston University have discovered a serious vulnerability in the Bluetooth communication protocol in Apple and Microsoft gadgets that allows attackers to track and identify devices. Vulnerabilities are subject to Mac, iPhone, iPad and Apple Watch, as well as Microsoft tablets and laptops. Devices running Android are not affected.
Gadgets use public Bluetooth advertising channels to announce their presence to other devices. For security, most of them broadcast a random address that changes periodically. The researchers found that this information is enough to extract identifying tokens that allow you to track the device even after changing a random address.
The algorithm does not require decrypting messages or violating the security of the Bluetooth protocol, since it is completely based on public unencrypted advertising traffic.
Devices running iOS or macOS have two identifying tokens that change at different intervals. On many devices, the values of identifying tokens change synchronously with the address. In some cases, the token change does not occur at the same moment, which allows the transfer algorithm to identify the next random address.
Android devices use protocols other than Microsoft and Apple for advertising traffic, so they are protected from data tracking methods.
In their report, the researchers also recommend companies to change the advertising protocol algorithms and synchronize the intervals of identifying tokens.
Editorial actualapple.com leads the channel in “Yandex. Dzen.” Subscribe!